Featured
Table of Contents
Ipsec (Internet Protocol Security)
For a full technical description of IPsec works, we recommend the exceptional breakdown on Network, Lessons. There are that figure out how IPsec customizes IP packets: Web Secret Exchange (IKE) develops the SA between the interacting hosts, working out the cryptographic secrets and algorithms that will be utilized in the course of the session.
The host that gets the package can use this hash to guarantee that the payload hasn't been modified in transit. Encapsulating Security Payload (ESP) secures the payload. It likewise includes a sequence number to the package header so that the receiving host can be sure it isn't getting replicate packages.
At any rate, both protocols are built into IP executions. The encryption established by IKE and ESP does much of the work we expect out of an IPsec VPN. You'll discover that we have actually been a little unclear about how the file encryption works here; that's due to the fact that IKE and IPsec allow a wide variety of encryption suites and innovations to be used, which is why IPsec has handled to survive over more than twenty years of advances in this location.
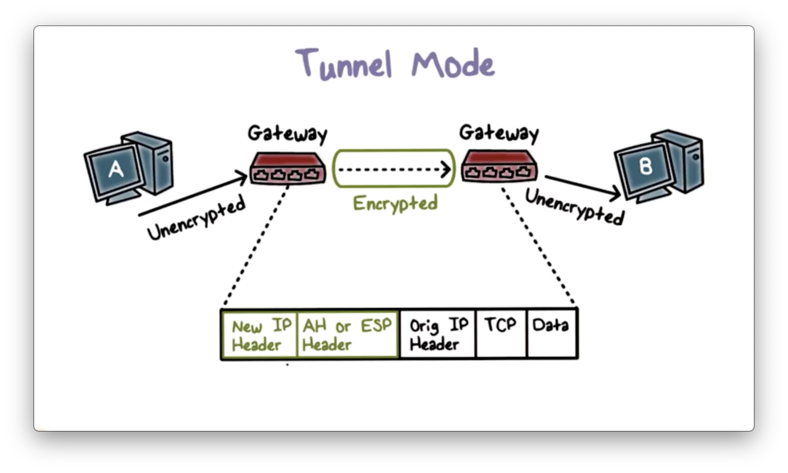
There are two various methods in which IPsec can operate, referred to as modes: Tunnel Mode and Transportation Mode. The difference in between the two refer to how IPsec deals with package headers. In Transport Mode, IPsec secures (or confirms, if only AH is being used) only the payload of the packet, however leaves the existing packet header data basically as is.
Ipsec: The Complete Guide To How It Works ...
When would you use the different modes? If a network package has actually been sent out from or is destined for a host on a private network, that packet's header includes routing data about those networksand hackers can evaluate that information and use it for dubious functions. Tunnel Mode, which secures that details, is typically used for connections in between the gateways that sit at the outer edges of private corporate networks.
Once it shows up at the entrance, it's decrypted and eliminated from the encapsulating packet, and sent out along its method to the target host on the internal network. The header information about the topography of the private networks is hence never ever exposed while the package passes through the general public web. Transport mode, on the other hand, is typically used for workstation-to-gateway and direct host-to-host connections.
On the other hand, since it utilizes TLS, an SSL VPN is protected at the transportation layer, not the network layer, so that might affect your view of how much it boosts the security of your connection. Where to read more: Copyright 2021 IDG Communications, Inc.
In brief, an IPsec VPN (Virtual Private Network) is a VPN running on the IPsec procedure. In this post, we'll describe what IPsec, IPsec tunneling, and IPsec VPNs are.
Ipsec: The Complete Guide To How It Works ...
IPsec stands for Web Protocol Security. In other words, IPsec is a group of protocols that set up a safe and encrypted connection between devices over the public web.
Each of those 3 different groups looks after different distinct tasks. Security Authentication Header (AH) it ensures that all the information originates from the very same origin which hackers aren't trying to pass off their own little bits of information as legitimate. Envision you get an envelope with a seal.

This is however one of two ways IPsec can run. The other is ESP. Encapsulating Security Payload (ESP) it's a file encryption protocol, suggesting that the information plan is transformed into an unreadable mess. Aside from encryption, ESP is similar to Authentication Headers it can authenticate the data and inspect its stability.
On your end, the encryption takes place on the VPN customer, while the VPN server takes care of it on the other. Security Association (SA) is a set of requirements that are agreed upon between two devices that establish an IPsec connection. The Internet Key Exchange (IKE) or the key management protocol is part of those requirements.
What Is Ipsec? - How Ipsec Vpns Work
IPsec Transportation Mode: this mode encrypts the information you're sending out however not the details on where it's going. While harmful actors couldn't read your obstructed interactions, they could inform when and where they were sent out. IPsec Tunnel Mode: tunneling creates a safe and secure, enclosed connection between two gadgets by utilizing the same old web.
A VPN using an IPsec procedure suite is called an IPsec VPN. Let's state you have an IPsec VPN client running. You click Link; An IPsec connection starts using ESP and Tunnel Mode; The SA establishes the security parameters, like the kind of encryption that'll be utilized; Data is prepared to be sent out and gotten while encrypted.
MSS, or maximum section size, describes a value of the optimum size an information package can be (which is 1460 bytes). MTU, the maximum transmission unit, on the other hand, is the value of the maximum size any device connected to the web can accept (which is 1500 bytes).
And if you're not a Surfshark user, why not become one? We have more than simply IPsec to offer you! Your personal privacy is your own with Surfshark More than simply a VPN (Web Secret Exchange variation 2) is a protocol utilized in the Security Association part of the IPsec protocol suite.
Ipsec Vpn Explained - How Ipsec Works - Ipsec Vs Ssl
Cybersecurity Ventures expects international cybercrime expenses to grow by 15 percent each year over the next 5 years, reaching $10. 5 trillion USD each year by 2025, up from $3 trillion USD in 2015. And, cyber attacks are not limited to the personal sector - government companies have actually suffered substantial data breaches.

Some may have IT programs that are out-of-date or in need of security patches. And still others simply might not have an adequately robust IT security program to resist progressively sophisticated cyber attacks. Considering these aspects, it is easy to see why third-party suppliers are a prime target for cybercrime.
As revealed in the illustration listed below, Go, Quiet secures the connection to enterprise networks in an IPSec tunnel within the business firewall program. This enables for a fully safe and secure connection so that users can access corporate programs, missions, and resources and send out, store and obtain details behind the safeguarded firewall software without the possibility of the connection being intercepted or hijacked.
Web Procedure Security (IPSec) is a suite of procedures generally utilized by VPNs to produce a secure connection online. The IPSec suite provides functions such as tunneling and cryptography for security purposes. This is why VPNs mostly use IPSec to produce safe and secure tunnels. IPSec VPN is likewise extensively known as 'VPN over IPSec.' IPSec is normally executed on the IP layer of a network.
Latest Posts
The Best Vpns To Protect Yourself Online
Smartphone Vpns: What You Need To Know
The 5 Best Vpn Services For The Bay Area